Is the Infrastructure Access Security Gap Putting You at Risk?


Written by
Dominic GarciaLast updated on:
October 11, 2022Reading time:
Some might say humans are the weak link in information security, but prominent data breaches show otherwise. Early in 2021, retail chain Hobby Lobby identified a security breach that impacted over 300,000 users and exposed 138GB of data – everything from names and phone numbers to the last four digits of customers’ payment cards. In 2019, a security incident resulted in 10.7 million MGM guests’ data being leaked, including names, addresses, and phone numbers. And back in 2018, 150 million MyFitnessPal users had their accounts compromised.
The common element in all these data breaches is access control. As one security expert noted from the MyFitnessPal breach, “trust but verify” isn’t enough when data is stored in the cloud and accessed from locations outside a company’s secured internal network. The infrastructure access security gap has only expanded with the rise of remote work and increased numbers of connected systems.
Organizations are turning toward Zero Trust principles to secure their infrastructure. With access and identity being two critical points to adopt Zero Trust, it’s not a surprise that 80 percent of companies have an Access Management initiative planned for the next year, according to our recent survey 2022: The Year of Access.
Legacy Access Practices Increase Risks
Unfortunately, many organizations are still using legacy access practices for their infrastructure. An overwhelming number of respondents to the study – 93 percent – have granted technical staff access to sensitive infrastructure, indicating how infrastructure has been democratized. But at what cost?
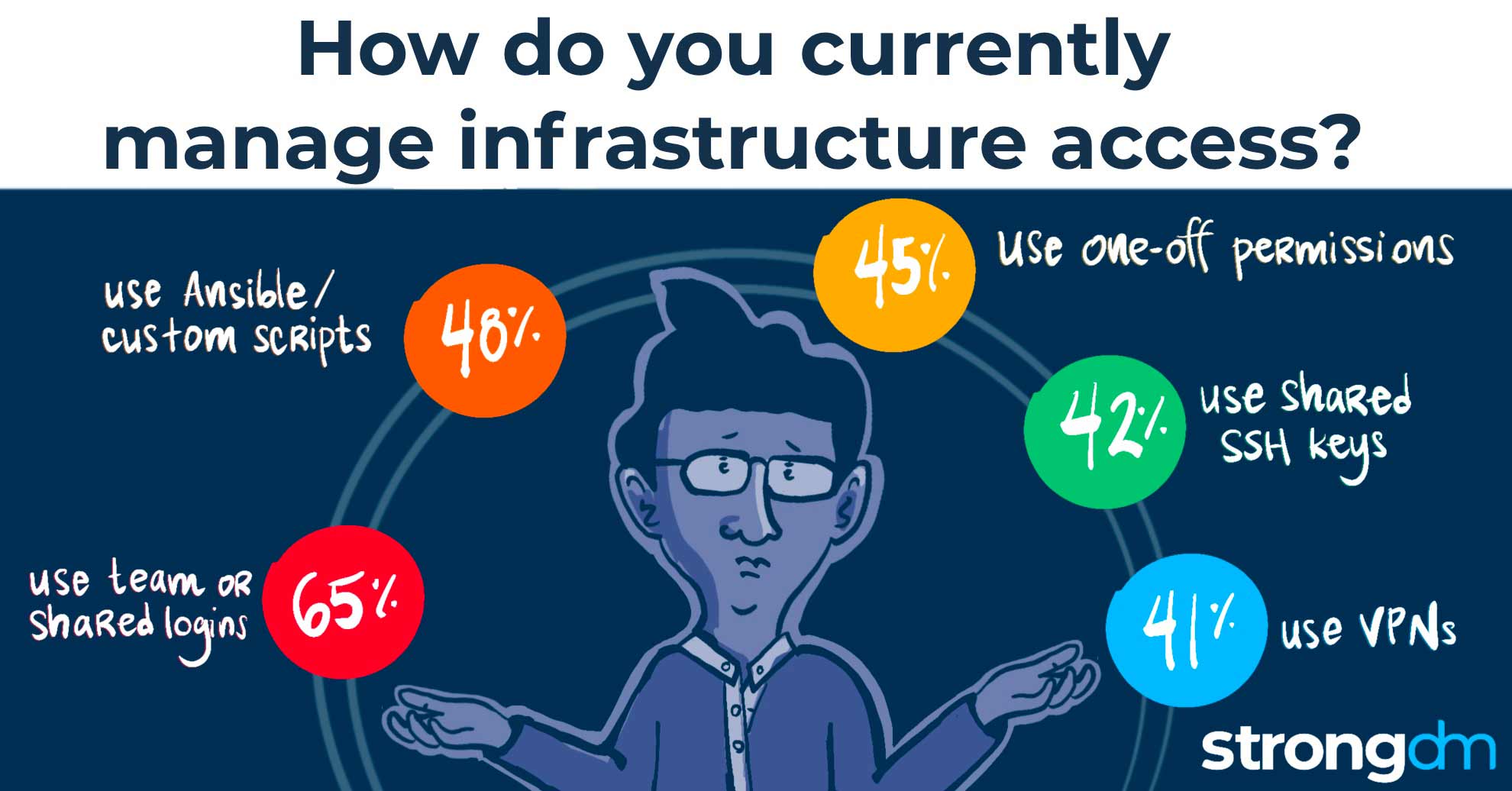
Nearly two-thirds (65 percent) use shared logins, and 42 percent rely on shared SSH keys. These practices make it hard to track who is accessing your systems. It could be a developer with a legitimate reason – or it could be a disgruntled former employee or malicious actor with plans to sell sensitive customer data on the dark web to the highest bidder.
Many companies use shared logins and shared SSH keys because they’re easy. Otherwise, they’d have to manually approve access for each person and each system. That’s not a big deal for a small company with just a few databases. But the average organization is provisioning dozens of databases and systems to many more users, everyone from in-house application developers to third-party partners. Half of the survey respondents noted that it can take hours, days, or even weeks to approve user access since these requests go through several layers of approvals.
Building a Modern Bridge for Infrastructure Access
Organizations aren’t using legacy technology anymore, and they need to let go of their legacy infrastructure access approval systems. As your company grows, you’ll add more systems, more databases, and more users. A modern approach that leverages automation and role-based access can help bridge the infrastructure access security gap, keeping sensitive data where it belongs.
For example, think of the one-off permissions you might grant a third-party partner to develop an application to monitor a segment of your supply chain. The app stalls in development, and eventually, you terminate the relationship. You’ll also want to terminate access or risk leaving a gaping hole for hackers to probe and exploit. An automated system could shut off access as soon as the project is finished.
And that’s just one of many ways that you can use automation to bridge the infrastructure access security gap and lessen the risk of a headline-making data breach – while still making sure your employees and partners have everything they need.
If you’re ready to ditch the legacy approvals for an approach that keeps your data secure, schedule your free demo of StrongDM today.
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough

Categories:

About the Author
Dominic Garcia, Technical Marketing Expert, has held marketing leadership roles for Silicon Valley technology companies specializing in database, data management, and data analytics solutions. As head of content marketing at Splunk, Dominic contributed to boosting the company’s market visibility and its growth from a $100M to a $1.3B company. He brings relentless creativity to the task of connecting people with technical products to improve their lives. Dominic holds a B.S. degree in Public Relations from the University of Texas at Austin. To contact Dominic, visit him on LinkedIn.
You May Also Like




