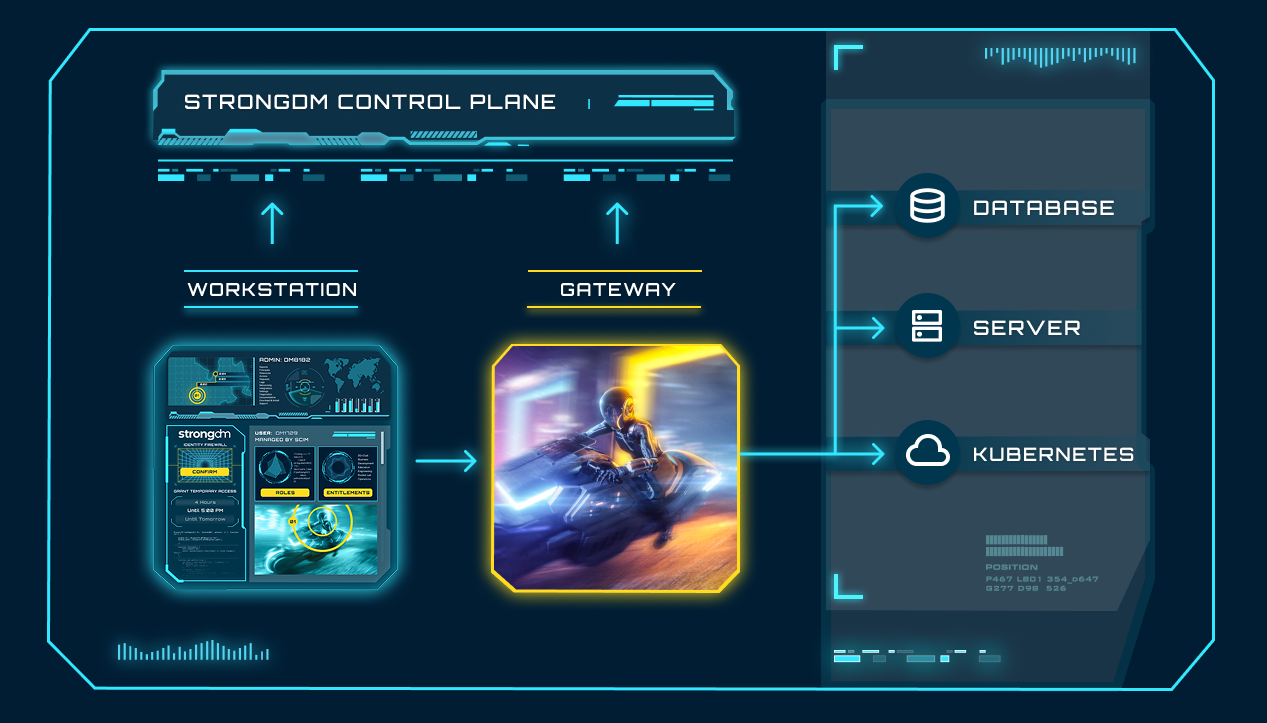

The local client tunnels requests from the user’s workstation to the gateway, through a single TLS 1.2-secured TCP connection. StrongDM supports Mac, Windows, and Linux workstations.
To authenticate, users login to the local client; that call can be optionally redirected to your identity provider or SSO.
The local client consists of both graphical and command-line interfaces.
Gateways are the entry point to your network. They can be deployed with a DNS entry, sit privately on the corporate network, and/or behind a VPN.
In the case of a flat network, it is the gateway that talks to the target systems. If internal subnets disallow ingress, relays create a reverse tunnel to form connections to the gateway. All data routes through your network.
Gateways decrypt credentials on behalf of end users, and deconstruct requests for the purposes of auditing.
Gateways and relays are deployed in pairs, and scale horizontally.
Gateways are the entry point to your network. They can be deployed with a DNS entry, sit privately on the corporate network, and/or behind a VPN.
In the case of a flat network, it is the gateway that talks to the target systems. If internal subnets disallow ingress, relays create a reverse tunnel to form connections to the gateway. All data routes through your network.
Gateways decrypt credentials on behalf of end users, and deconstruct requests for the purposes of auditing.
Gateways and relays are deployed in pairs, and scale horizontally.
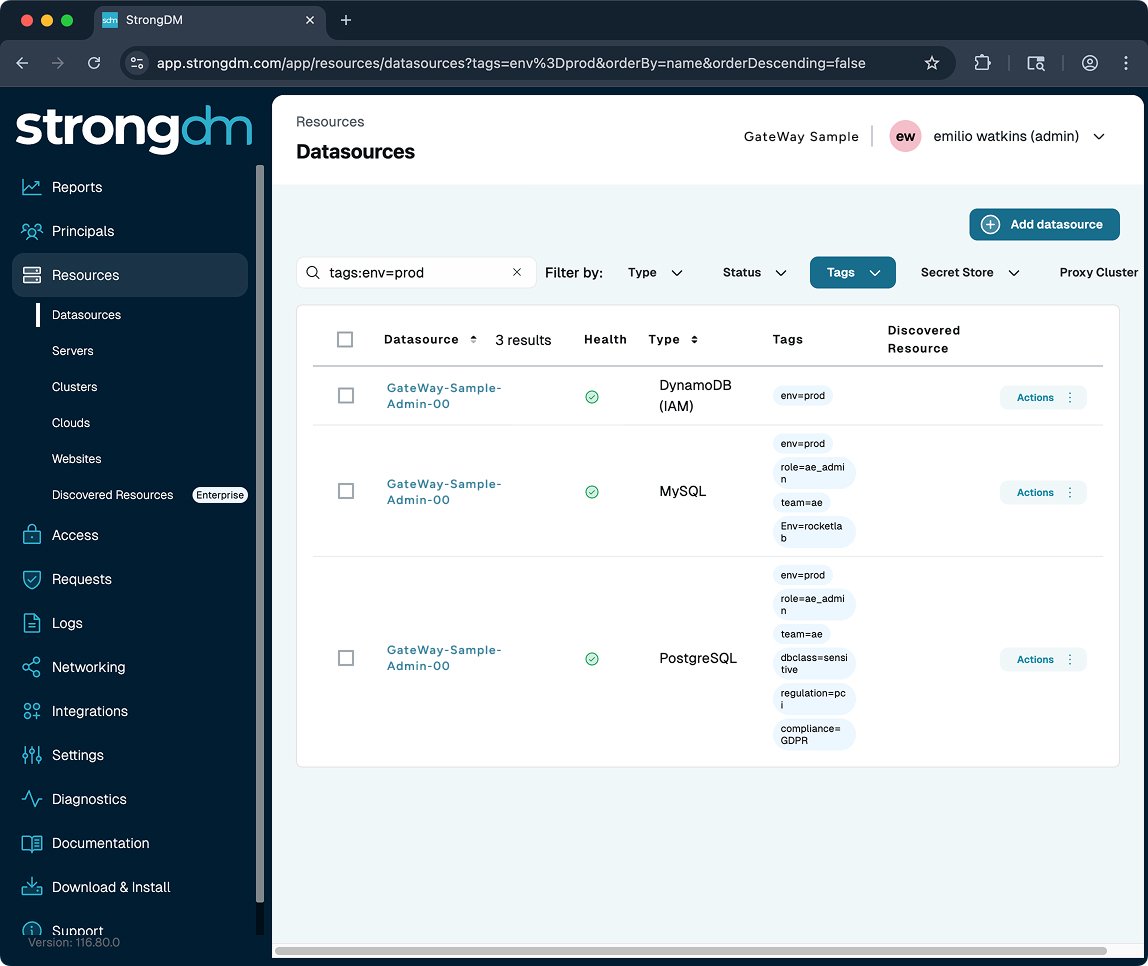
The Admin UI houses configuration. Users are assigned to roles, and roles are collections of permissions across servers, databases, clusters, and web apps. Configuration is pushed down to the end user's local client, and updated in real-time.
Trusted by:

Zero Trust means that determining whether a user (person or machine) should have access to a system or data needs to be assessed throughout every session, not only when they attempt access.
Using risk-based assessment, access needs to be severed immediately if trust is no longer achieved.
_HighPerformer_Mid-Market_Americas_HighPerformer.png?width=155&height=178&name=IdentityandAccessManagement(IAM)_HighPerformer_Mid-Market_Americas_HighPerformer.png)
_HighPerformer_Americas_HighPerformer.png?width=155&height=178&name=IdentityandAccessManagement(IAM)_HighPerformer_Americas_HighPerformer.png)
_Leader_Leader.png?width=155&height=178&name=PrivilegedAccessManagement(PAM)_Leader_Leader.png)
_UsersMostLikelyToRecommend_Small-Business_Nps.png?width=155&height=179&name=PrivilegedAccessManagement(PAM)_UsersMostLikelyToRecommend_Small-Business_Nps.png)
_BestSupport_Small-Business_QualityOfSupport.png?width=155&height=178&name=PrivilegedAccessManagement(PAM)_BestSupport_Small-Business_QualityOfSupport.png)
_EasiestToUse_Small-Business_EaseOfUse.png?width=155&height=178&name=PrivilegedAccessManagement(PAM)_EasiestToUse_Small-Business_EaseOfUse.png)
_EasiestToDoBusinessWith_Small-Business_EaseOfDoingBusinessWith.png?width=155&height=178&name=PrivilegedAccessManagement(PAM)_EasiestToDoBusinessWith_Small-Business_EaseOfDoingBusinessWith.png)
_Leader_Mid-Market_Leader.png?width=155&height=178&name=PrivilegedAccessManagement(PAM)_Leader_Mid-Market_Leader.png)
