Written by
John MartinezLast updated on:
October 15, 2025Reading time:
Proofpoint is a SaaS based cybersecurity and compliance company that purchased Meta Networks in 2019. Proofpoint ZTNA (Meta Networks) is a Zero Trust Network Access provider that specializes in granting secure remote access from a user level. They focus heavily on providing users with the ability to securely access company resources from any location while ditching the need for a VPN. However, if you're looking for a simple and secure way, without expensive starting costs and required add-ons, Proofpoint might not be the best solution to fit your needs. In this post, we go over a few Proofpoint alternatives and the pros and cons of each.
Proofpoint Overview
Brief product summary
Proofpoint was designed to replace the need for a VPN. Built within the cloud in a user-centric approach to zero trust. Proofpoint provides secure remote access to applications and network resources. It also offers granular access to reduce overall security exposure and grants user permissions to specific applications. It gives remote users the ability to retain the same level of security during any internet access and not just on the corporate network. Developed as an “always-on” VPN, Proofpoint allows users to access whatever they need from wherever they are while eliminating the need for multiple VPNs. Centralized access from all locations.
Use cases
- Zero trust network access.
- Zero trust application access.
- Remote access from any location.
Pluses
- Defined perimeter from the user level.
- Replaces the need for a VPN.
- Cloud-based and secure remote access.
- Provides users the ability to maintain similar levels of security outside of the corporate network.
- Works on-prem and in the cloud.
- Defends against phishing and spam email threats.
Minuses
- Complex administrative portal.
- Expensive starting costs.
- No comprehensive options, must buy add-ons for more robust security.
- UI lacking in richness.
- Limited manual report exports.
- Clunky monitoring rules for email sequencing.
1. StrongDM
Brief product summary
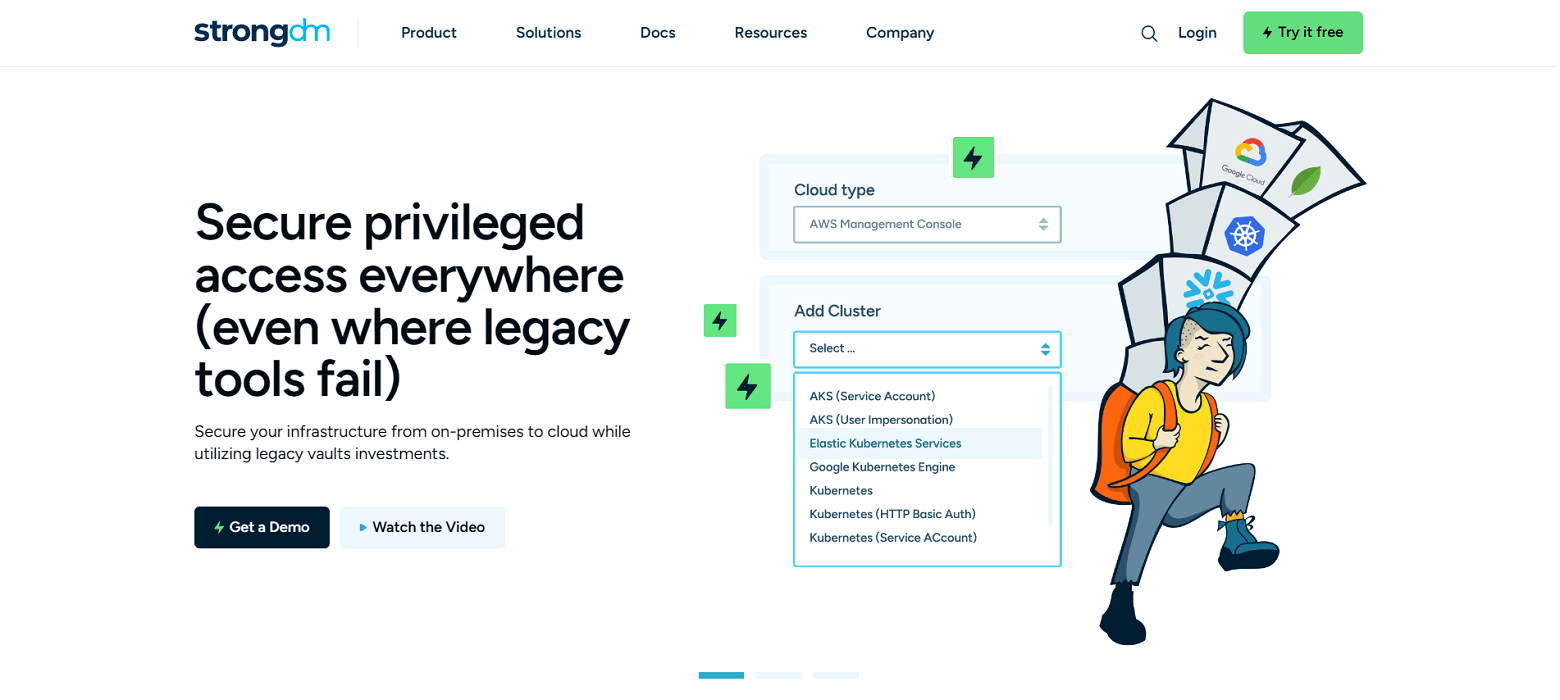
StrongDM is a control plane to manage and monitor access to databases, servers, and Kubernetes. Their zero trust model means instead of distributing access across a combination of VPN, individual database credentials, and SSH keys, StrongDM unifies user management in your existing SSO (Google, Onelogin, Duo, Okta, SAML, etc...) and keeps the underlying credentials hidden. Neither credentials nor keys are accessible by end users. Because StrongDM deconstructs every protocol, it also logs all database queries, complete SSH and RDP sessions, and kubectl activity.
Use cases
- Faster onboarding- no need to provision database credentials, ssh keys, VPN passwords for each new hire.
- Secure off-boarding- suspend SSO access once to revoke all database, server access.
- Automatically adopt security best practices- least privilege, just-in-time access, audit trail.
- Comprehensive observability and visibility- log every permission change, database query, ssh & kubectl command.
- Vendor privileged access management-connect third-party vendors to resources with project-based access that automatically expires.
- Security and compliance teams-simplify HIPAA, SOC 2, SOX, ISO 27001 compliance certification.
- Modern Cloud PAM solution-built to support a variety of cloud networks, including public, private, multi-cloud, and hybrid.
Pluses
- Easy deployment - self-healing mesh network of proxies.
- No change to workflow- use any SQL client, CLI, or desktop BI tool.
- Standardize logs across any database type, Linux or Windows server, and Kubernetes.
- Graphical client for Windows and MacOS.
- See and replay all activity with session recordings.
- Manage via a user-friendly web browser interface.
- Simple, straightforward pricing.
Minuses
- Requires continual access to StrongDM API for access to managed resources.
StrongDM Reviews
- 4.8 / 5 stars: Read all of StrongDM’s G2 reviews.
- StrongDM's expert rating.
Pricing Information
StrongDM offers simple pricing, including support for all resource types.
Users have the option to sign up for a free 14-day trial.
2. Delinea (formerly Thycotic & Centrify)
Brief product summary
Delinea’s Privilege Manager is a tool that allows organizations to secure access for privileged administrators (typically systems and database administrators) to Windows Servers, Linux servers, and some database management systems via a centralized authentication method. Delinea does not secure access to modern and cloud-native databases, Kubernetes clusters, cloud CLIs, switches, routers, or internal web applications.
Use cases
- Centralized access to Linux and Windows servers, and some legacy databases.
Pluses
- SSH access available.
- RDP access available.
- Authenticates users via LDAP and Active Directory (AD).
- Integrates with some machine groups.
- Cloud and on-premise deployable.
- Simpler pricing.
Minuses
Delinea is designed for legacy systems and highly privileged administrators. It is designed for Windows-based environments and does best with legacy databases and authentication methods (AD, LDAP). Delinea is not designed for any cloud-native environments, newer database management systems, nor modern infrastructure tooling like Kubernetes, Docker, and ephemeral environments). Finally, it does not cover all users within a company, most of whom require access to systems that contain privileged information (for example, financial analysts who might need access to transactional information).
3. BeyondTrust
Brief product summary
BeyondTrust offers a suite of products under their brand name. Those include Endpoint Privilege Management, Password Safe, Privileged Remote Access, DevOps Secret Safe and Remote Support. BeyondTrust Endpoint Privilege Management allows users to approve and revoke access to critical systems while providing an audit trail for admins to track end user behavior and monitor or approve custom integrations. Password Safe allows end users and admins to manage the use and access of privileged credentials and SSH keys while also offering auditing and analytics capabilities for further security. DevOps Secret Safe is similar in that it provides centralized secrets management but utilizes REST APIs and CLI tools to streamline development workflows and allow for seamless API integrations. Privileged Remote Access provides vendors and remote workers a more secure way to access their workstations including internal and external cloud infrastructure. It eliminates the need for a VPN and provides the benefits of PAM from a remote environment. Remote Support provides IT with the ability to remotely monitor, access, and control any customer devices on or off the corporate network. This also includes a video log to audit behaviors while also seamlessly integrating with external directories like LDAP.
Use cases
- Implement least privilege across Unix and Linux severs.
- Enforce least privilege on Windows and MacOS.
- Audit and secure privilege account credentials.
- Control remote access.
- Extend PAM principles to network and cloud environments.
Pluses
- SSH access available.
- RDP available.
- Host of apps within the BeyondTrust family.
- Established in the endpoint security industry since 1985.
- Manage permissions with AD, LDAPS, RADIUS & Kerberos.
Minuses
- No comprehensive solutions.
- Need to purchase add-ons.
- Complex initial setup.
- Very high licensing costs.
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough


About the Author
John Martinez, Technical Evangelist, has had a long 30+ year career in systems engineering and architecture, but has spent the last 13+ years working on the Cloud, and specifically, Cloud Security. He's currently the Technical Evangelist at StrongDM, taking the message of Zero Trust Privileged Access Management (PAM) to the world. As a practitioner, he architected and created cloud automation, DevOps, and security and compliance solutions at Netflix and Adobe. He worked closely with customers at Evident.io, where he was telling the world about how cloud security should be done at conferences, meetups and customer sessions. Before coming to StrongDM, he lead an innovations and solutions team at Palo Alto Networks, working across many of the company's security products.
You May Also Like