Written by
John MartinezLast updated on:
September 29, 2025Reading time:
Tailscale is a zero-configuration virtual private cloud that builds secure networks for WireGuard-encrypted traffic. Tailscale replaces traditional VPNs with a coordination node that acts as a control plane to manage keys and identities. This allows you to create a secure network between cloud resources without the need for firewall configuration changes. However, if your goal is to centralize and secure access to databases, servers, Kubernetes, and more, a VPN (even a fancy modern one) may not be the best approach. In this blog post, we’ll look at the strengths and weaknesses of a few Tailscale alternatives.
Tailscale Overview
Brief product summary
Tailscale is open-source software that scales from single-user networks to enterprise environments. It integrates with your existing identity provider, making it easy to enforce multi-factor authentication and off-board users who no longer need access.
Tailscale relies on WireGuard for tunneling and encryption. When connecting, the client configures its own WireGuard instance with a pair of randomly generated private and public keys. The public key carries identity information, while the private key always remains with the client—allowing Tailscale to establish a zero-trust network.
Use cases
- Connect personal computing environments.
- Create secure point-to-point connections.
- Facilitate remote access from any physical location.
- Establish and enforce security access policies.
- Manage large-scale deployments.
Pluses
- Easy to configure and use.
- Provides audit-compliant logging.
- Integrates with your existing identity provider.
- Works with teams of any size.
- Protects your credentials with automatic key rotation.
- Command-line clients are open source.
Minuses
- Requires some networking expertise.
- The product is still in an early growth phase.
- RBAC is only available at higher-tier pricing.
- Okta integration is only available at higher-tier pricing.
- SAML SSO integration is only available at higher-tier pricing.
1. StrongDM
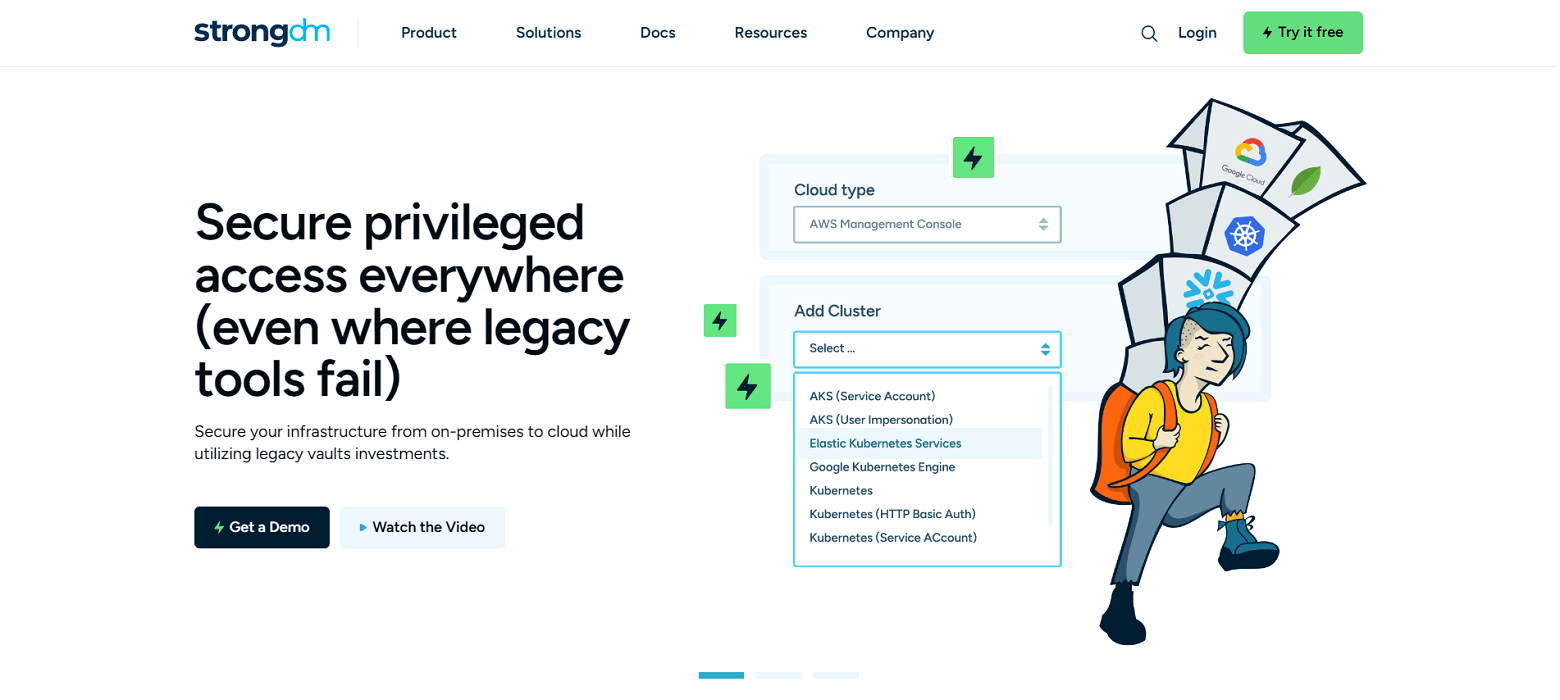
Brief product summary
StrongDM is a control plane to manage and monitor access to databases, servers, and Kubernetes. Their zero trust model means instead of distributing access across a combination of VPN, individual database credentials, and SSH keys, StrongDM unifies user management in your existing SSO (Google, Onelogin, Duo, Okta, SAML, etc...) and keeps the underlying credentials hidden. Neither credentials nor keys are accessible by end users. Because StrongDM deconstructs every protocol, it also logs all database queries, complete SSH and RDP sessions, and kubectl activity.
Use cases
- Faster onboarding- no need to provision database credentials, ssh keys, VPN passwords for each new hire.
- Secure off-boarding- suspend SSO access once to revoke all database, server access.
- Automatically adopt security best practices- least privilege, just-in-time access, audit trail.
- Comprehensive observability and visibility- log every permission change, database query, ssh & kubectl command.
- Vendor privileged access management-connect third-party vendors to resources with project-based access that automatically expires.
- Security and compliance teams-simplify HIPAA, SOC 2, SOX, ISO 27001 compliance certification.
- Modern Cloud PAM solution-built to support a variety of cloud networks, including public, private, multi-cloud, and hybrid.
Pluses
- Easy deployment - self-healing mesh network of proxies.
- No change to workflow- use any SQL client, CLI, or desktop BI tool.
- Standardize logs across any database type, Linux or Windows server, and Kubernetes.
- Graphical client for Windows and MacOS.
- See and replay all activity with session recordings.
- Manage via a user-friendly web browser interface.
- Simple, straightforward pricing.
Minuses
- Requires continual access to StrongDM API for access to managed resources.
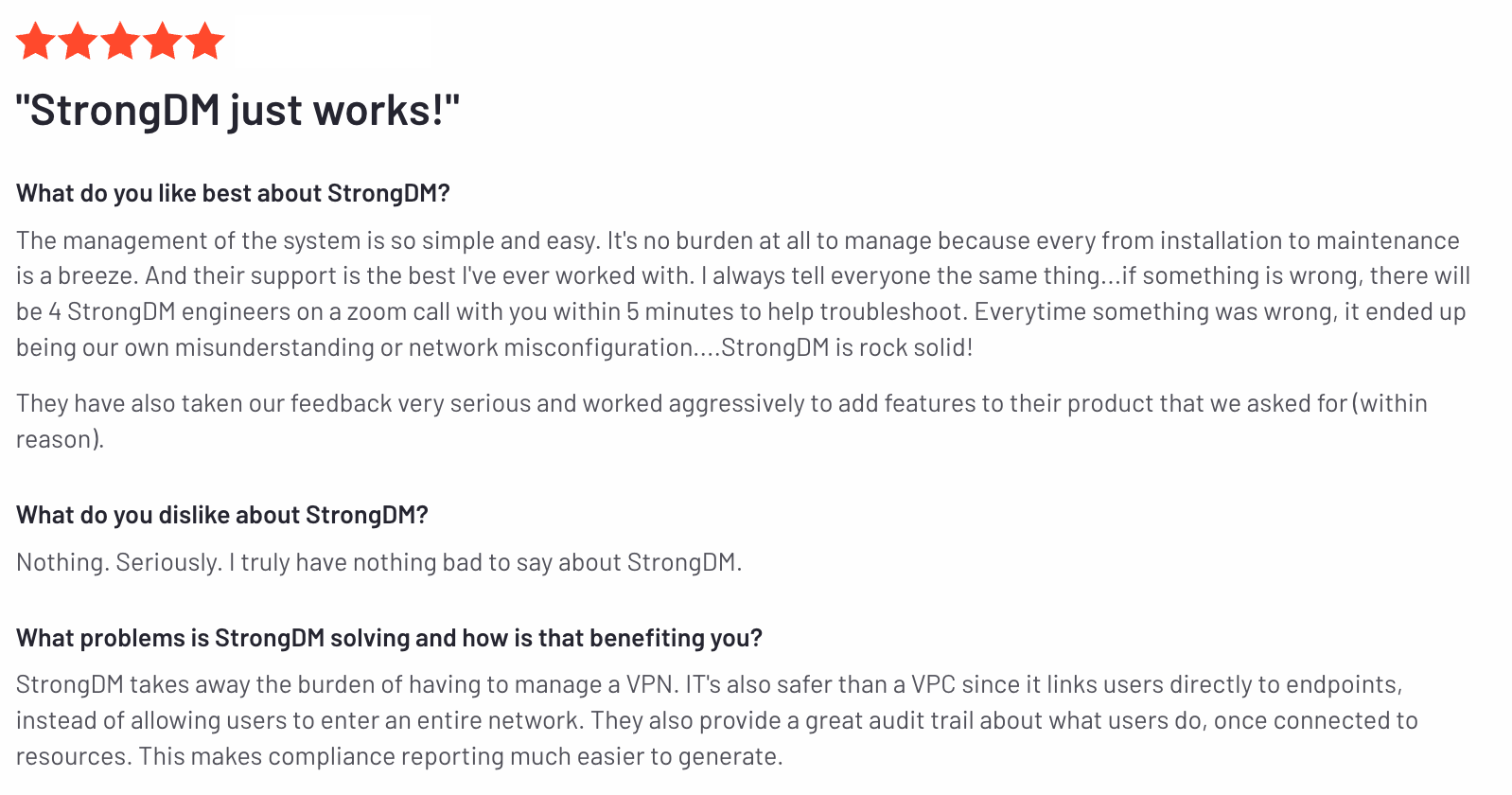
StrongDM’s G2 Reviews
- 4.8 / 5 stars
Read all of StrongDM’s G2 reviews here.
Pricing Information
StrongDM offers simple pricing, including support for all resource types.
Users have the option to sign up for a free 14-day trial.
2. Okta ASA
Brief product summary
Okta's Advanced Server Access (ASA), formerly ScaleFT, is a tool allowing organizations to secure access to SSH and RDP servers via a centralized authentication method.
Use cases
- Centralized access to SSH and RDP servers.
Pluses
- SSH access is available.
- RDP access is available.
- Single sign-on (SSO) for SSH/RDP and your identities in Okta.
- Authorized requests leverage single-use client certificate or web token scoped to the user and resource being accessed.
Minuses
- Okta’s software must be running on every server it manages access to.
- Complex setup: in addition to the ScaleFT software on each server, a ScaleFT Gateway and ScaleFT local client must also be built and maintained for each cluster.
- CLI-only client scares off non-engineers.
- User credentials are assigned ephemerally adding complexity to deployments and uptime.
- Backend configuration required to export audit logs to any 3rd-party.
- ScaleFT agent audit logs are only accessible through an early access enablement.
- Audit logs only cover SSH.
- No auditing for RDP.
- Complex pricing model.
- Pricing based per server, which gets extremely expensive in ephemeral environments or those with high-n servers.
3. Teleport (Community Edition or Enterprise)
Brief product summary
Gravitational Teleport provides privileged access management (PAM) for cloud-native infrastructure. Teleport is an access and authentication proxy for SSH and Kubernetes API access. It's meant as a replacement for sshd and it works with existing OpenSSH clients and servers as-is. It allows administrators to set up access for users and groups to groups of servers, called clusters, and implements role-based access control (RBAC) to allow differing levels of access to different clusters. Individual server credentials are not available to users, reducing the administrative impact of rotating and removing credentials.
The open source Community Edition of Teleport is the same as the Enterprise edition, with the following exceptions:
No RBAC.
No SSO integration.
No paid support is available.
Use cases
- Centralized access to servers and Kubernetes.
- Granting user SSH access to the same usernames across a cluster of servers.
Pluses
For the Enterprise Edition:
- SSH access available via web UI on proxy server.
- Single sign-on (SSO) for SSH/Kubernetes and your organization identities via Github Auth, OpenID Connect or SAML with endpoints like Okta or Active Directory.
- Can use with an existing OpenSSH infrastructure.
- Teleport uses SSH certificate-based access with automatic certificate expiration time.
Minuses
For the Enterprise Edition:
- Teleport software must be running on every server to be managed by Teleport access.
- Complex setup: in addition to the Teleport software on each server, a Teleport Proxy and TeleportAuth server must also be built and maintained for each cluster.
- CLI-only client scares off non-engineers.
- User credentials are assigned across a full cluster rather than server-by-server.
- Backend configuration required to store audit logs (AWS S3 / DynamoDB, required by teleport to store session logs).
- Teleport agent audit logs are only accessible through the UI or backend storage.
- Complex pricing model.
For the Community Edition:
- Because it’s available free, only community support is available.
- Is missing important enterprise features (see above).
- Only uses local users or Github for identity-based authentication.
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough


About the Author
John Martinez, Technical Evangelist, has had a long 30+ year career in systems engineering and architecture, but has spent the last 13+ years working on the Cloud, and specifically, Cloud Security. He's currently the Technical Evangelist at StrongDM, taking the message of Zero Trust Privileged Access Management (PAM) to the world. As a practitioner, he architected and created cloud automation, DevOps, and security and compliance solutions at Netflix and Adobe. He worked closely with customers at Evident.io, where he was telling the world about how cloud security should be done at conferences, meetups and customer sessions. Before coming to StrongDM, he lead an innovations and solutions team at Palo Alto Networks, working across many of the company's security products.
You May Also Like