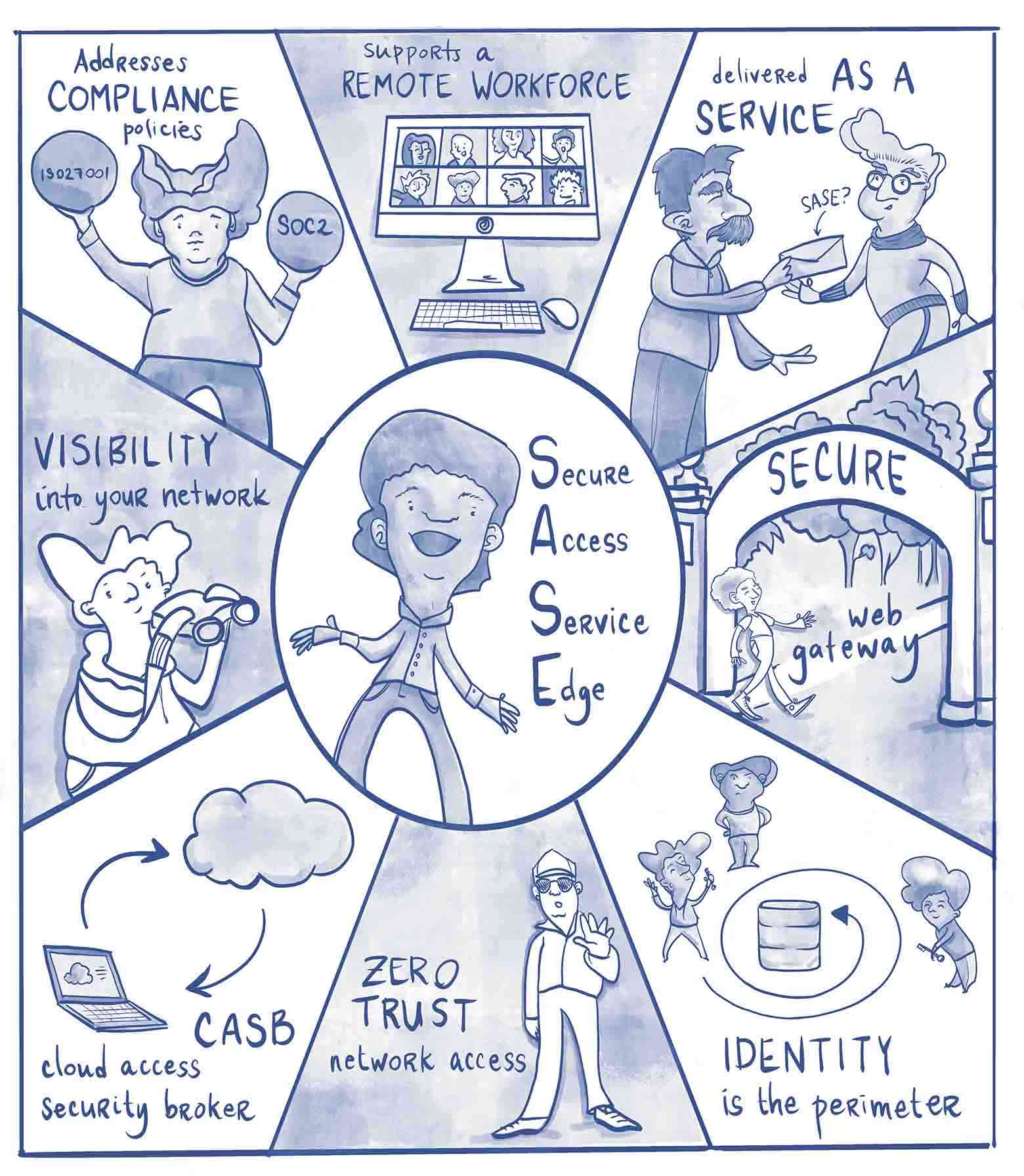
Secure Access Service Edge is an increasingly popular security solution for enterprises today. In fact, Gartner predicts that by 2025, at least 60% of enterprises will have explicit strategies and timelines for SASE adoption encompassing user, branch, and edge access—up from 10% in 2020.
So what makes it so great? Here are 11 key benefits of adopting this model:
1. Centralized and dynamic RBAC
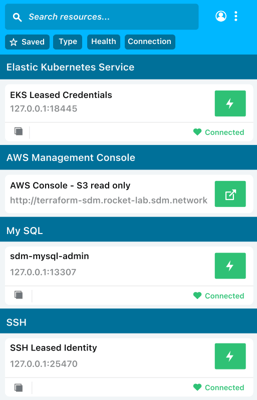
SASE relies on centralized role-based access control (RBAC), which restricts access based on a user’s role within the organization. Roles are assigned by the company and determine the permissions and access each user is granted through the system.
For example, roles might include administrators, specialists, and end-users—each with varying levels of access or permissions. Some employees may have permission to access and modify documents, while others can only view the files.
This allows organizations to secure access in a more targeted and flexible way. With RBAC, employees can only access information that is necessary to do their jobs—limiting the number of people who can access or share sensitive data within the company.
2. Bird’s-eye-view across hybrid environments
SASE unifies your network management, giving you a centralized, bird’s-eye-view across all your hybrid environments. As organizations increasingly move into the cloud, security environments have become more complex, requiring disparate tools and management solutions to piece them all together. This creates blind spots in data and network management, leaving organizations vulnerable.
SASE solves the problem of siloed data and tools by bridging those technology gaps and bringing network and security management under one seamless umbrella.
3. Governance of users, apps, and data usage
By unifying the security technology stack, the SASE model improves the overall governance of users, applications, and data usage.
It ensures best practice security solutions (including RBAC, DLP, FWaaP, and SWG) are applied across all environments, eliminating gaps in the security perimeter and enforcing consistent policy and compliance no matter where the user is or how they are accessing data.
4. Audit trail and reporting
Data monitoring and reporting is an essential component of network security. Relying on machine learning and artificial intelligence, the SASE model builds audit trail and reporting mechanisms into the network architecture to ensure comprehensive visibility and real-time, scalable threat prevention, detection, and analysis at every touchpoint in a hybrid environment.
5. Simplified security model
One of the biggest benefits of SASE is that it simplifies the cloud and hybrid security model. Legacy network solutions require additional tools and systems to keep up with the pace of digitalization, the expansion of attack surfaces, and emerging security threats. However, legacy solutions often fall short of the advanced capabilities today’s modern IT needs to protect their organizations.
The result: increasingly complex security environments and a growing technology stack that doesn’t always work together.
SASE addresses this challenge by applying FWaaS, which embeds security features like URL filtering, anti-malware, and firewalling into its infrastructure. This simplifies security management, enabling organizations to set and enforce uniform policies, identify issues quickly, and secure all edges with consistent protection.
6. Consistent edge-to-edge security
SASE combines network and security functions within a single multi-tenant cloud platform that strengthens security and performance. As part of a full network security stack, the solution embeds advanced security functionalities such as SWG, NGFW, and DLP into its architecture, enabling edge-to-edge protection.
7. Cost reduction
SASE eliminates the need for disjointed physical and virtual appliances from multiple vendors. This reduces costs to adopt and maintain disconnected solutions while simplifying ongoing management from the backend. Reducing complexity further improves cost savings by minimizing the workload for IT, increasing efficiency, and reducing staffing costs—all without sacrificing security.
8. Less administrative effort and time
SASE simplifies network security management through one central cloud-based application. Which means the architecture doesn’t grow in complexity when the network expands. This reduces the administrative workload and frees up time for IT staff to focus on other high-value priorities.
9. Reduced dependencies
The SASE model provides an elegant solution that reduces an organization’s dependencies on multiple appliances and vendors. Not only does this minimize costs and resource investments, but it also gives the organization greater control and flexibility over its network infrastructure and edge security.
10. Faster and more reliable service
SASE replaces traditional VPN appliances with network security based on ZTNA principles. With traditional VPN point solutions, enterprises must deploy additional appliances to fill gaps in functionality (like SD-WAN security and NGFW).
VPN appliances often become bottlenecks that slow down a WAN, negatively impacting performance because they have CPU and resource limitations. The cloud-native SASE solution isn’t limited by scale and delivers additional WAN optimization through its underlying infrastructure, enabling faster and more reliable service.
11. Perpetual data protection
Today, companies collect, process, and distribute massive volumes of data—including sensitive proprietary and personal data. In order to protect data across environments, SASE enables DLP delivery through the cloud, essentially eliminating the need for adopting and maintaining multiple protection tools. This allows organizations to apply consistent security policies at all edges, from mobile devices to the cloud, to on-premise locations.