Alternatives to ManageEngine PAM360

Written by
John MartinezLast updated on:
September 29, 2025Reading time:
ManageEngine’s PAM360 gives system administrators a centralized way to manage and audit user and privileged accounts within network resources. It also tracks and analyzes unusual privileged activity through artificial intelligence (AI) and machine learning (ML) capabilities. However, teams that need to manage secure access to Kubernetes environments or enforce password policies within their privileged access management (PAM) system may want to consider other options. This blog post will cover ManageEngine PAM360 alternatives, along with the pros and cons of each.
ManageEngine PAM360 Overview
Brief product summary
A business unit of Zoho Corp, ManageEngine offers numerous IT, DevOps, and cybersecurity solutions, including its PAM360 privileged access management (PAM) platform. PAM360 provides tools that enable granular control and monitoring of users within critical network resources and assets. These tools apply to IT system administrators who maintain and protect technology assets and DevOps engineers who secure development environments.
PAM360 also offers features that help privileged users streamline workflows for validation ticketing, Secure Sockets Layer (SSL) certificate management, and Secure Socket Shell (SSH) key management.
Use cases
- Integrates with Microsoft Active Directory (AD) for centralized machine identity, credentials, and user management
- Protects teams against credential-based attacks throughout DevOps processes
- Provides system visibility with anomaly detection, user activity tracking, and AI behavior analysis
⚠️ Traditional PAM deployments have gaps. Learn how to protect your databases, the cloud, Kubernetes, and more with our legacy PAM augmentation guide.
Pluses
- Offers just-in-time controls and remediation for privileges and account permissions
- Provides simplified auditing and compliance reporting for activity data
- Includes preventive, detective, and remediation privileged security features
- Integrates with SSL certificate management systems, such as Digicert™ and GoDaddy™
Minuses
- Offers no solutions for incorporating organizational policies and standards into user password management requirements
- Cannot manage secure access to Kubernetes or other data container systems
1. StrongDM
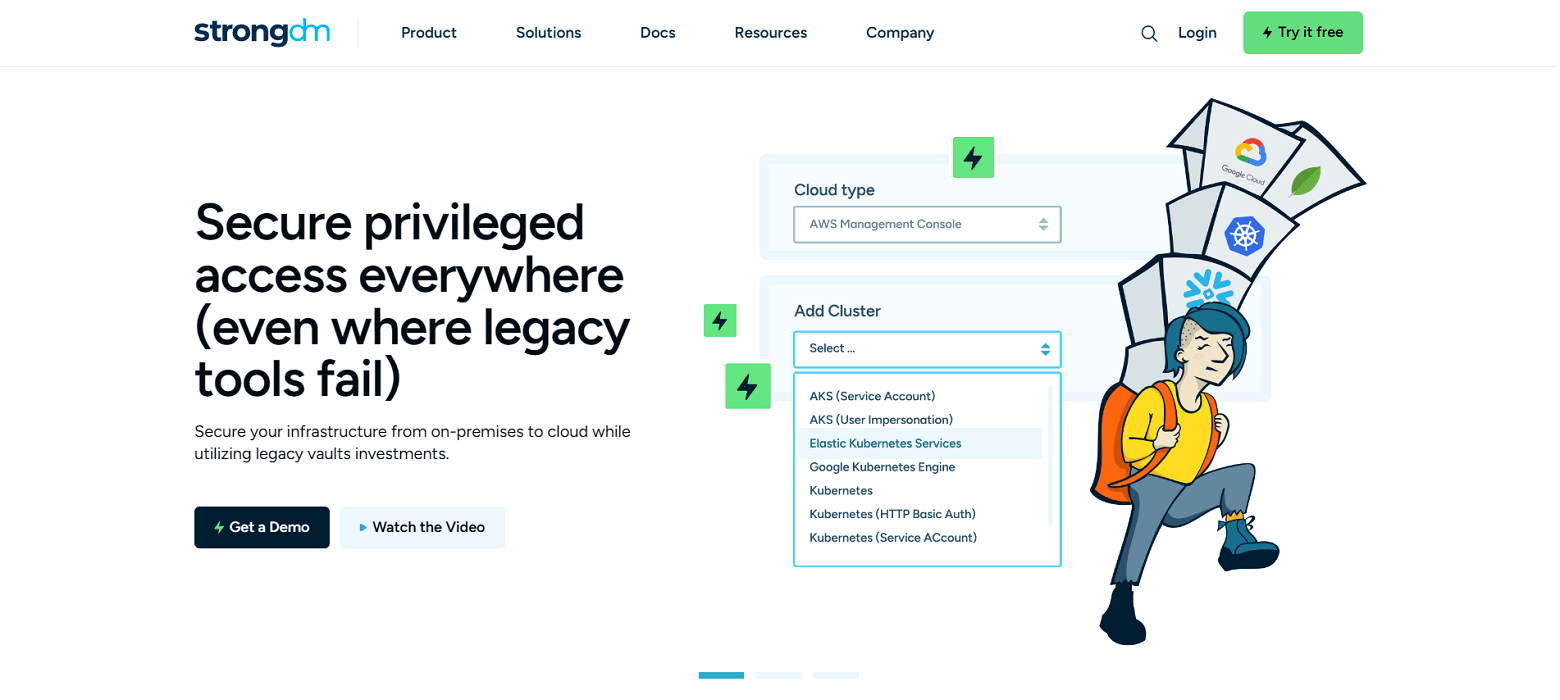
Brief product summary
StrongDM is a Zero Trust PAM platform that lets administrators and security leaders manage accessibility to databases, servers, web apps, and Kubernetes systems. It acts as a single source of truth to automate user provisioning workflows while securing verification with multi-factor authentication (MFA), role-based access control (RBAC), and enforcement of protected session types, including SSH and Microsoft Remote Desktop Protocol (RDP).
Use cases
- Simplifies user onboarding through instant, granular resource provisioning with temporary privilege authentication
- Facilitates streamlined offboarding with one-click removals and single sign-on (SSO) suspension
- Enables automated least privilege and policy enforcement
- Provides robust query commands, session replay, web activity, and application request monitoring with data logging to manage audits
- Vendor privileged access management-connect third-party vendors to resources with project-based access that automatically expires
- Security and compliance teams-simplify HIPAA, SOC 2, SOX, ISO 27001 compliance certification
- Modern Cloud PAM solution-built to support a variety of cloud networks, including public, private, multi-cloud, and hybrid
Pluses
- Simple platform deployment with no server installation requirements, plus an easy-to-navigate interface
- Wide range of resource types for protected access management and logging, which include SSH, databases, Kubernetes, and cloud services like Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP)
- Excellent platform usability attributes supplemented by exceptional customer support
- Standard and transparent pricing model, which includes all features in one plan
- A solid solution for developing and enforcing Zero Trust Network Access (ZTNA)
Minuses
- Requires continuous access to StrongDM’s Application Programming Interface (API) to access managed resources, forcing organizations to rely on StrongDM’s system for security management and resource accessibility
StrongDM’s G2 Reviews
- 4.8 / 5 stars
Read all of StrongDM’s G2 reviews here.
Pricing Information
StrongDM offers simple pricing, including support for all resource types.
Users have the option to sign up for a free 14-day trial.
2. CyberArk PAM
Brief product summary
Founded in the late 1990s, CyberArk has been a prominent provider of identity security and access management solutions. Its Privileged Access Manager tool is well-suited for enterprise-level businesses that use legacy systems, including
- Windows or Linux servers
- Databases, such as Oracle, Microsoft Structured Query Language (SQL) Server, or IBM’s Db2
- Lightweight Directory Access Protocol (LDAP) directories
With CyberArk, system administrators can manage and track encryption keys, remote access, user accounts, sessions, governance policies, and resource privileges with cloud, on-premises, and hybrid deployments.
Use cases
- Controls and tracks privileged and non-privileged network sessions
- Secures, leases, and administers privileged credentials through a password vault
- Provides RBAC for Linux and Windows servers and Oracle, DB2, and SQL databases
- Ensures enterprise security policy governance and enforcement through the PAM system
Pluses
- Allows for cloud, on-premises, and hybrid deployments
- Enables privileged users and administrators to enforce organizational policies (such as password requirements) within the PAM using the Master Policy tool
- Provides authentication through Active Directory, LDAP servers, Security Assertion Markup Language (SAML), or Remote Authentication Dial-in User Service (RADIUS)
- Allows for RDP and web SSH sessions and comes with audit logging plus session replays
Minuses
- Its outdated interface can be difficult to navigate and operate, leading to poor user experiences (UX)
- A complex deployment process that requires direct installation on customer servers
- Lack of secure access management for Kubernetes or other data container systems
- CyberArk has a complex and opaque pricing model
3. JumpCloud IAM & Device Management Platform
Brief product summary
JumpCloud is a modern-day solution that combines a cloud directory tool with an identity, access, and device management platform in a single system. It can administer SSO, MFA, and RBAC security controls, includes a credential vault for privileged users, and performs activity logging for detection and audit reporting purposes. The subscription options are relatively cost-friendly, divided by specific modules and features, such as user provisioning, SSO configuration, identity and access management, and Zero Trust turnkey implementation.
Use cases
- Delivers end-to-end lifecycle management for machine identities, devices, applications, and other network resources
- Simplifies user onboarding, offboarding, and privileged access provisioning
- Offers network and server authentication through RADIUS and cloud LDAP
- Provides activity and events data tracking, logging, and reporting
- Enables identity-based authentication for Zero Trust architecture
- Offers APIs and cloud directory-based integration with Active Directory, Google Workspace, and Microsoft 365
Pluses
- Well-known for its usability when setting up, operating, and administering with no hardware or separate maintenance required by the IT staff
- Offers control management features necessary for Zero Trust and industry standards, including General Data Protection Regulation (GDPR), Payment Card Industry Data Security Standard (PCI DSS) compliance, Service Organization Control 2 (SOC 2), and the Health Insurance Portability and Accountability Act (HIPAA)
- Works with a wide range of usable operating systems, including Windows, Mac, and Linux
- Offers a free plan for up to ten users and devices
Minuses
- No session replay, recording, or playback features
- Limited customer support for the free version
- No automated or customizable approval workflows
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough


About the Author
John Martinez, Technical Evangelist, has had a long 30+ year career in systems engineering and architecture, but has spent the last 13+ years working on the Cloud, and specifically, Cloud Security. He's currently the Technical Evangelist at StrongDM, taking the message of Zero Trust Privileged Access Management (PAM) to the world. As a practitioner, he architected and created cloud automation, DevOps, and security and compliance solutions at Netflix and Adobe. He worked closely with customers at Evident.io, where he was telling the world about how cloud security should be done at conferences, meetups and customer sessions. Before coming to StrongDM, he lead an innovations and solutions team at Palo Alto Networks, working across many of the company's security products.
You May Also Like