Written by
John MartinezLast updated on:
June 26, 2025Reading time:
Saviynt is a popular identity and access management (IAM) solution, but it may not be the best choice for every organization. In this article, we’ll explore powerful alternatives to Saviynt for companies with cloud-first IT infrastructure. By the end of this article, you’ll have a better idea of whether Saviynt or one of these Saviynt competitors is the right fit for you.
Saviynt Overview
Brief product summary
Saviynt is a cloud-native, enterprise IAM solution that specializes in supporting identity governance and administration (IGA). Saviynt’s privileged access management (PAM) standards and granular access controls for applications help organizations solve common security and regulatory compliance concerns when enterprises are moving from on-premises solutions to the cloud.
Use cases
Saviynt is most appropriate for enterprise organizations ready to transition from legacy Identity Governance and Administration (IGA) software. For companies with many on-premises solutions that are looking to accelerate their transition to the cloud, Saviynt can help them develop a foundation for adopting zero trust architecture while controlling risk across their application ecosystem and simplifying security controls.
This solution can also support companies with:
- Maintaining identity governance standards in multi-cloud environments
- Enabling productivity with automation to improve workforce identity management
- Managing machine identities in alignment with zero trust principles
- Meet ever-changing compliance standards
Pluses
- Provision user access anywhere, any time across any application
- Close access security gaps and automatically find risky identities with analytics powered by AI and machine learning
- Detect cross-application segregation of duty (SoD) conflicts and unexpected violations easily
- Simple implementation and user-friendly interface
Minuses
- Limited integrations and not supportive of customizations
- Limits the number of logs accessible within a 24-hour period
- Customers report performance issues when Saviynt tries to process data across applications
- Costly licensing fees
1. StrongDM
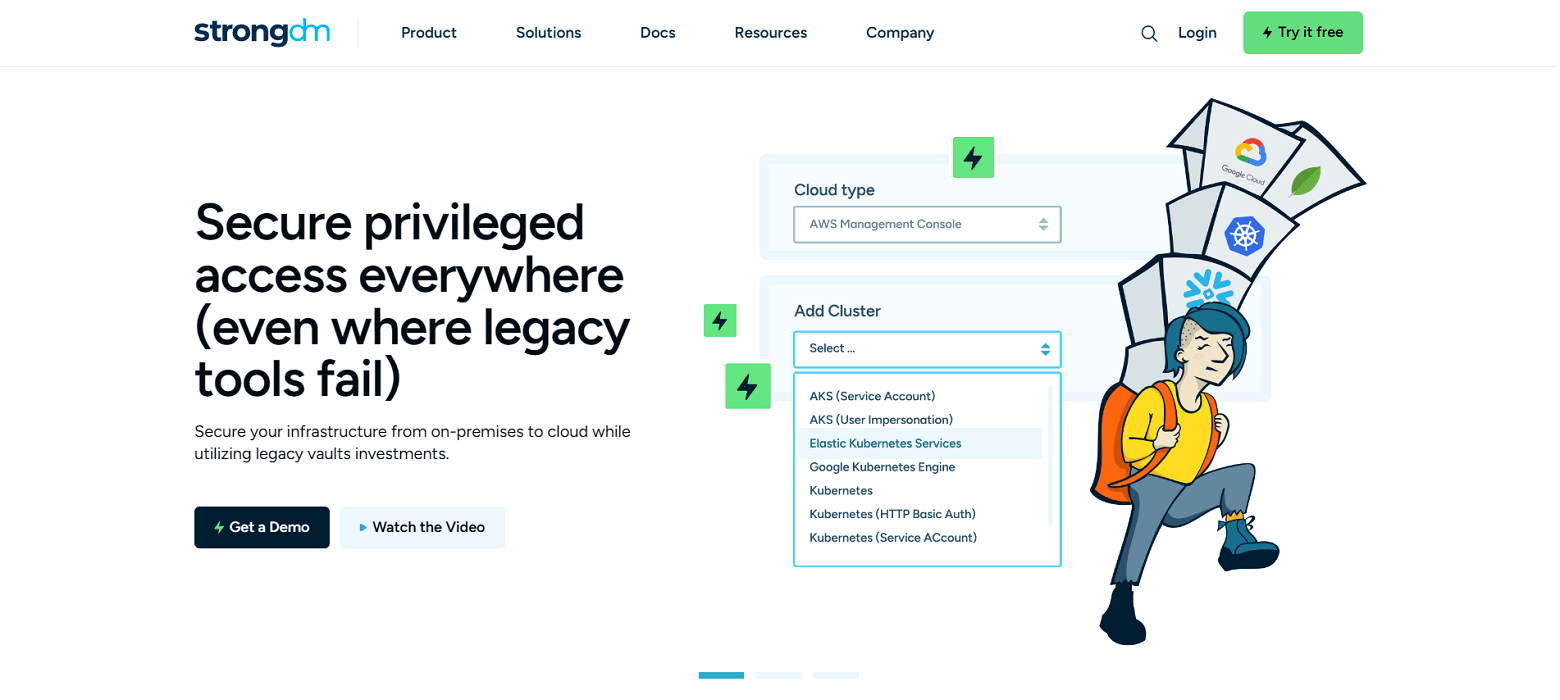
Brief product summary
StrongDM is a control plane to manage and monitor access to databases, servers, clusters, and web apps. StrongDM's zero trust model means instead of distributing access across a combination of VPN, individual database credentials, and SSH keys, StrongDM authenticates users with your existing SSO (Google, Onelogin, Okta, SAML, etc...) and authorizes access to infrastructure based on identity. Access is group or role-based, keeping the underlying credentials hidden from end users.
StrongDM logs every event, and it also logs all database queries, complete SSH and RDP sessions, and kubectl activity. This makes it one of the strongest Saviynt competitors on the market.
Use cases
- Faster onboarding- no need to provision database credentials, ssh keys, VPN passwords for each new hire
- Secure off-boarding- suspend SSO access once to revoke all database, server access
- Automatically adopt security best practices- least privilege, just-in-time access, audit trail
- Comprehensive observability and visibility- log every permission change, database query, ssh & kubectl command
- Vendor privileged access management-connect third-party vendors to resources with project-based access that automatically expires
- Security and compliance teams-simplify HIPAA, SOC 2, SOX, ISO 27001 compliance certification
- Modern Cloud PAM solution-built to support a variety of cloud networks, including public, private, multi-cloud, and hybrid
Pluses
- Easy deployment and management
- No change to workflow - use any SQL client, CLI, or desktop BI tool
- Standardize logs across any database type, Linux or Windows server, and Kubernetes
- Graphical client for Windows and macOS
- See and replay all activity with session recordings
- Manage via a user-friendly web browser interface
- Centralized control pain to access infrastructure across your entire stack
- Simple, straightforward pricing
Minuses
- Requires continual access to StrongDM API for access to managed resources
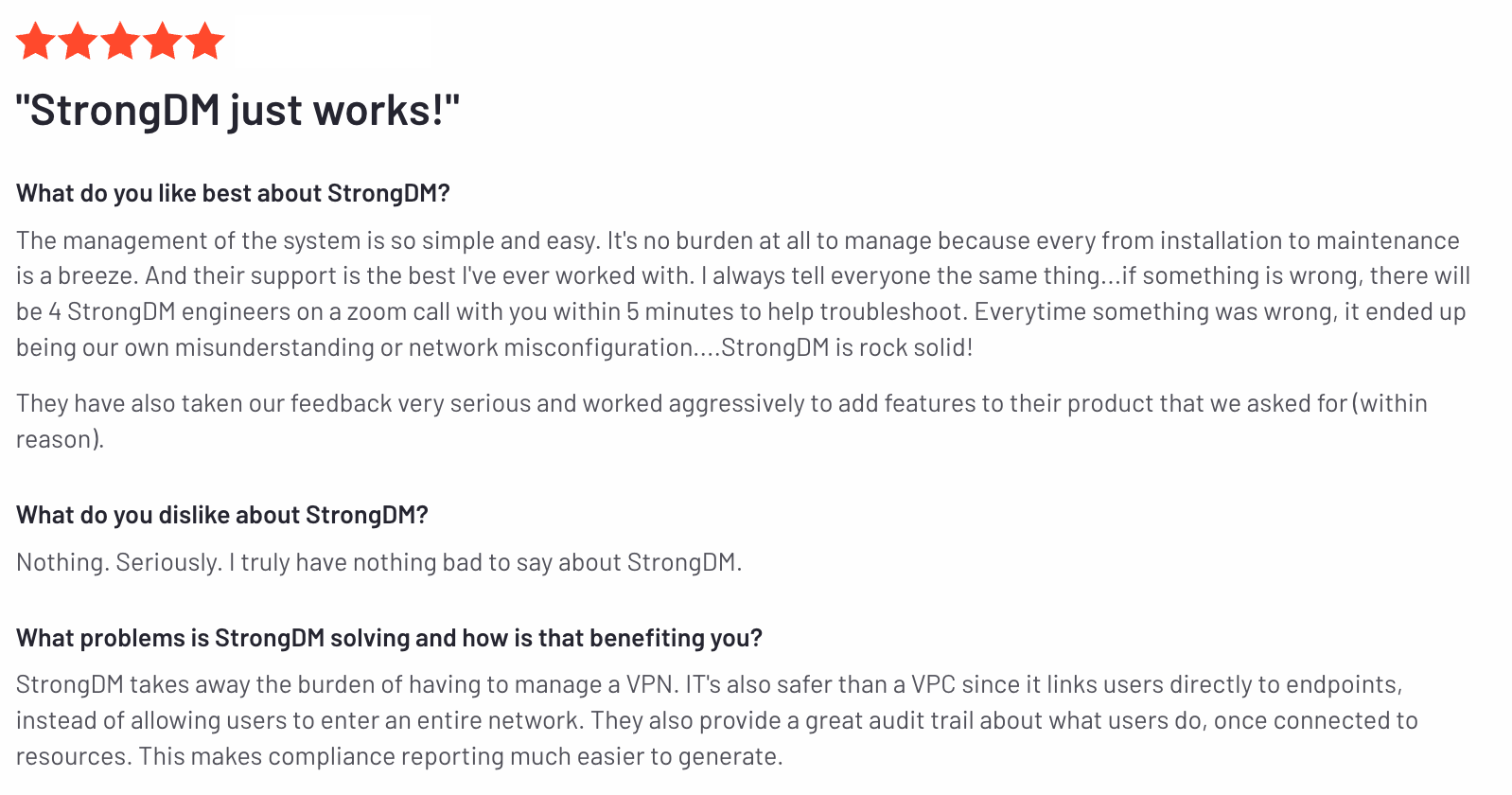
StrongDM’s G2 Reviews
- 51 reviews (at the time of writing)
- 4.8 / 5 stars
Read all of StrongDM’s G2 reviews here.
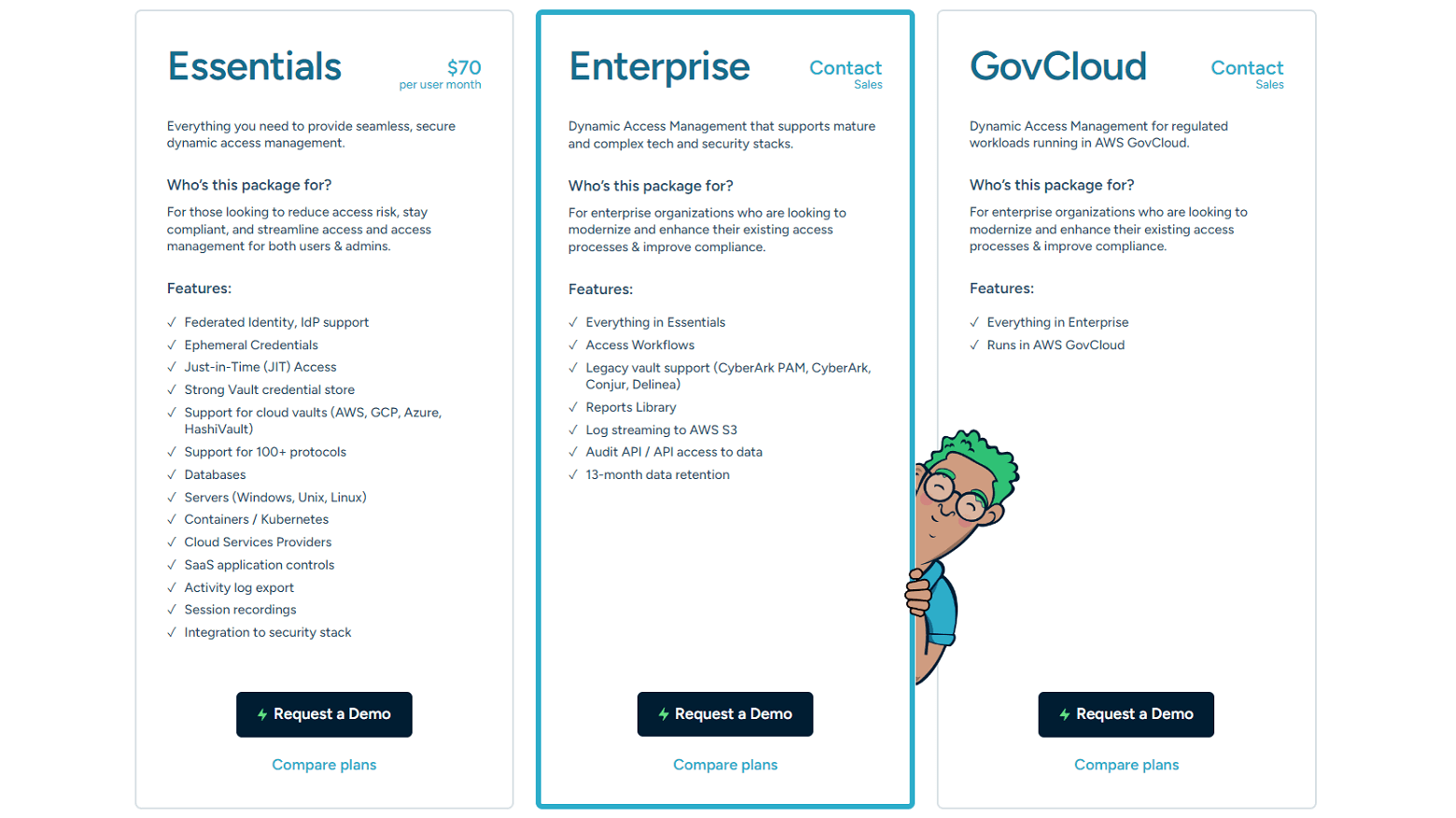
Pricing Information
StrongDM offers simple per-user pricing, starting at $70/license, including support for all resource types.
Users have the option to sign up for a free 14-day trial.
2. Okta ASA
Brief product summary
Okta started providing its Advanced Server Access product after acquiring ScaleFT in 2018. This PAM solution allows organizations to enable secure access and authentication for SSH and RDP servers in hybrid and multi-cloud environments. By grouping users into teams, Okta ASA offers role-based access control for companies to manage server access.
Use cases
Okta offers a wider range of products that companies can use together to develop more comprehensive IAM capabilities—including identity governance and workforce identity management—to align with similar solutions on the market and be a powerful Saviynt alternative.
Okta ASA specifically gives companies easier access management capabilities for SSH and RDP servers.
Pluses
- Gain access and authentication to SSH and RDP servers
- Enable single sign-on to strengthen identity management
- Control access with single-use client certificates or web tokens.
Minuses
- Limited solution only manages access to servers; other additions are necessary to manage extensive IT infrastructure
- Since the product must be set up and run on every server it manages, and pricing is by server, this solution can be expensive in certain environments
- Combining products to create a more comprehensive IAM solution can quickly become expensive
- Can’t audit RDP servers
- Logs for SSH servers aren’t easily accessible
- Ephemeral credentials can compromise uptime and add unnecessary complexity to deployments
3. CyberArk
Brief product summary
CyberArk’s Privileged Access Manager allows companies to track and manage access—and, more importantly, restrict access—to resources like SSH servers, RDP servers, and legacy databases. Organizations can access the Privileged Access Manager as both a SaaS offering and an on-premises solution, which may be preferable for their target audience: companies with Windows-heavy IT environments and legacy systems.
CyberArk also offers a variety of products for companies to enhance and expand their identity and access management.
Use cases
CyberArk supports organizations working with traditional server operating systems and older database management systems to provide access management and authenticate users through LDAP or Active Directory. It centralizes access to both SSH and RDP servers and some databases, but is not the best fit for supporting cloud environments.
While CyberArk do provide access to cloud accounts, their solutions aren’t designed to work with database management systems like Kafka and Redis or infrastructure tooling environments like Kubernetes and Docker.
Pluses
- Single, centralized page provides easy management for SSH and RDP servers and legacy databases
- Provides user authentication integration with LDAP and Active Directory (AD)
- Machine group integration
Minuses
- Designed and intended for legacy Windows environments and legacy authentication solutions, making it a poor fit for cloud-native infrastructure
- The CyberArk SaaS offering charges for licenses for each product and function individually, making on-premises adoption more cost-effective
- Ideal for managing access for privileged administrators, but not all users across the organization
- Requires extensive assistance to install, configure and maintain
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough


About the Author
John Martinez, Technical Evangelist, has had a long 30+ year career in systems engineering and architecture, but has spent the last 13+ years working on the Cloud, and specifically, Cloud Security. He's currently the Technical Evangelist at StrongDM, taking the message of Zero Trust Privileged Access Management (PAM) to the world. As a practitioner, he architected and created cloud automation, DevOps, and security and compliance solutions at Netflix and Adobe. He worked closely with customers at Evident.io, where he was telling the world about how cloud security should be done at conferences, meetups and customer sessions. Before coming to StrongDM, he lead an innovations and solutions team at Palo Alto Networks, working across many of the company's security products.
You May Also Like